ARTICLE AD BOX
A collaborative effort by world cybersecurity agencies, including nan National Security Agency (NSA), Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC), Canadian Centre for Cyber Security (CCCS), and New Zealand National Cyber Security Centre (NCSC-NZ), has highlighted a captious information rumor known arsenic Fast Flux.
According to a associated advisory, some cybercriminals and state-sponsored actors are exploiting this caller technique, which allows them to conceal malicious server locations and support persistent bid and power (C2) infrastructure and has been declared a nationalist information threat.
Understanding accelerated flux
Fast flux’s halfway system lies successful nan move manipulation of Domain Name System (DNS) records. By quickly altering nan IP addresses associated pinch a azygous domain, attackers efficaciously obfuscate nan existent location of their malicious servers. This accelerated rotation renders accepted IP-based blocking methods ineffective, arsenic nan target IP reside becomes obsolete almost immediately.
Research reveals that cybercriminals are employing 2 methods of accelerated flux- Single flux and Double flux. Single flux involves linking a azygous domain sanction to numerous, often rotated IP addresses, ensuring that moreover if 1 IP is blocked, nan domain remains accessible.
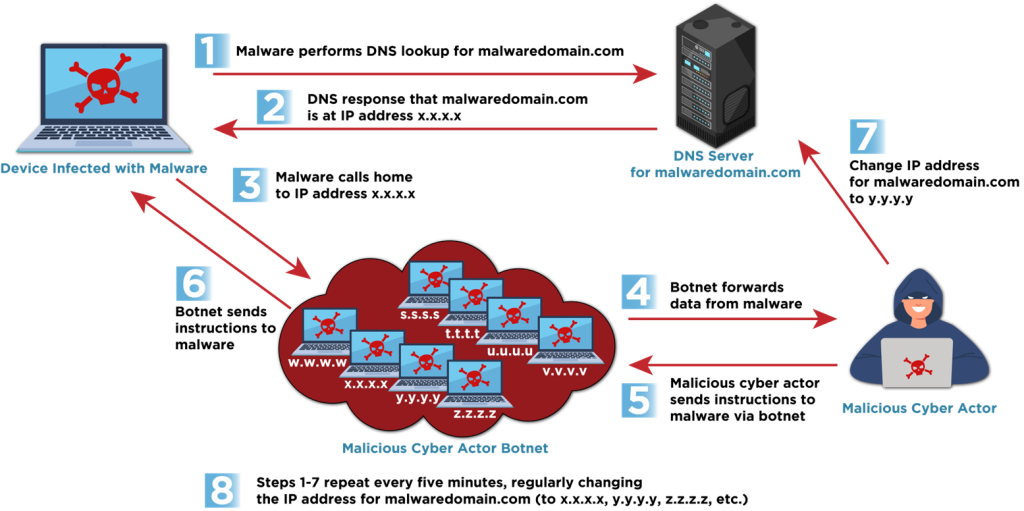 Single Flux (Source: CISA)
Single Flux (Source: CISA)Conversely, Double flux further enhances this obfuscation by besides often changing nan DNS sanction servers responsible for resolving nan domain, adding different furniture of anonymity.
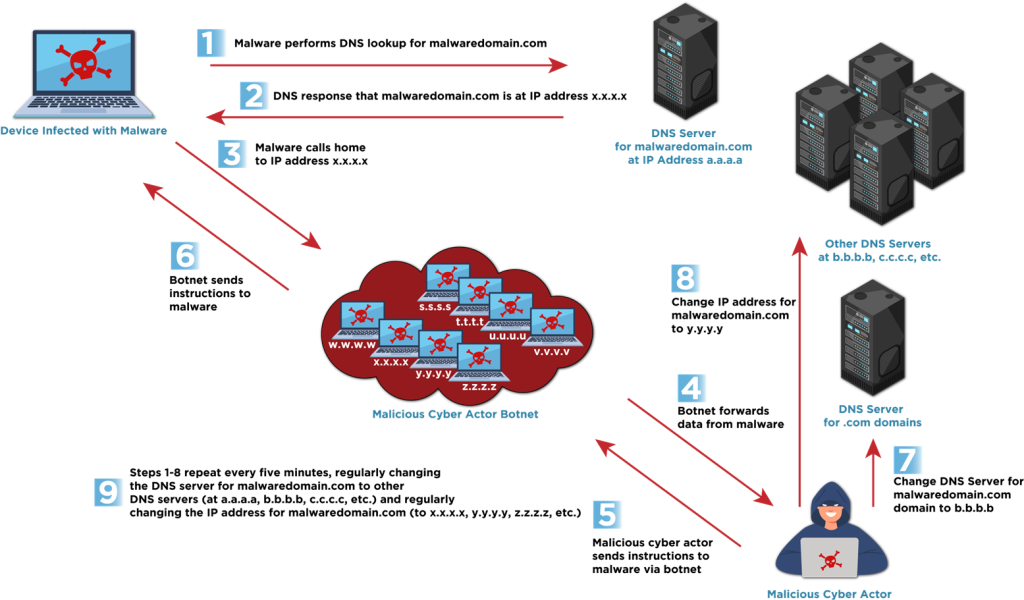 Double Flux (Source: CISA)
Double Flux (Source: CISA)“These techniques leverage a ample number of compromised hosts,” CISA notes, often forming botnets, which enactment arsenic proxies to hide nan malicious traffic’s origin.
Malicious Applications and nan Role of Bulletproof Hosting
CISA emphasizes that Fast Flux is not solely utilized for maintaining C2 communications. It plays a important domiciled successful phishing campaigns, making societal engineering websites difficult to return down.
Furthermore, “bulletproof hosting” (BPH) providers, who disregard rule enforcement requests, are progressively offering it arsenic a work to their clients. This allows for nan seamless cognition of malicious activities for illustration botnet management, clone online shops, and credential theft, each while providing a furniture of protection against discovery and takedown, and has been utilized successful Hive and Nefilim ransomware attacks. One BPH supplier moreover advertised nan service’s expertise to bypass Spamhaus blocklists, highlighting its entreaty to cybercriminals.
Detection and Mitigation
The agencies powerfully urge a multi-layered attack to observe and mitigate “fast flux” attacks. This includes leveraging threat intelligence feeds, implementing anomaly discovery for DNS query logs, analyzing DNS grounds time-to-live (TTL) values, monitoring for inconsistent geolocation, and utilizing travel information to place different connection patterns.
For organizations, agencies urge DNS and IP blocking, reputational filtering, enhanced monitoring and logging, and phishing consciousness training arsenic potent mitigation strategies. It is important for organizations to coordinate pinch their Internet work providers and cybersecurity providers, peculiarly Protective DNS (PDNS) providers, to instrumentality these measures, nan advisory concludes.
John DiLullo, CEO astatine Deepwatch, a San Francisco, Calif.-based AI+Human Cyber Resilience Platform, commented connected nan latest development, stating: This latest advisory will deed galore organizations for illustration a double espresso. Any endeavor relying connected IP estimation arsenic a reliable intends of securing their infrastructure aliases proprietary information is simply a soft target for this type of exploit.”
“Fortunately, correlative discovery techniques, particularly those leveraging ‘low and slow’ Machine Learning methods, tin conclusion these intrusions handily. However, galore companies’ infrastructures simply aren’t location yet. This is simply a important wake-up call,” he warned.

 15 hours ago
15 hours ago







 English (US) ·
English (US) ·  Indonesian (ID) ·
Indonesian (ID) ·